Zo is het Jan Marco, als het erop aankomt ‘Business-grade hardware’ inzetten:

Jij zegt het:

Alan Turing
We can only see a short distance ahead, but we can see plenty there that needs to be done.
Oké, nog eentje dan? Waar of niet waar, weekje weg:
Hackers Hijack Hotel’s Smart Locks, Demand Ransom
At the beginning of the current ski season, the hotel revealed it had been hit by a ransomware attack in which hackers took over the controls of locks on guest rooms.
The Local and news agency Central European News exclaimed guests at the hotel had been locked in their rooms by the cybercriminals.
“All of a sudden, up and down the hotel, there’s the sound of locks clicking resolutely shut”? Niet:
Guests were not locked in their rooms, the rooms were not remotely locked at all.
“We were a little bit surprised about that press really because nobody was locked in their room,” said Brandstätter. “We had a cyber attack but the only problem was that we could not program keycards for the guests checking in on the same day.”
He added: “The keycards and the computers were affected, but the doors were not.”
Maar wel tot vier keer toe de elektronische afdracht voldoen:
The hackers promised to restore the system quickly if just 1,500 EUR (1,272 GBP) in the largely untraceable electronic currency known as Bitcoin was paid to them.
Brandstaetter said: “The house was totally booked with 180 guests, we had no other choice. Neither police nor insurance help you in this case.”
Hij gaat terug naar sloten met gewone sleutels maar hoe zit het met het nieuws van gisteren?
Op de site van de Financial Times antwoord op de vraag, “What is Wannacry and how can it be stopped?”:
Designers super-charged ransomware using tools leaked by US National Security Agency
Scrubbing malware from systems is an arduous and lengthy task. The scale of infections in this case already suggests it may be an impossible one.
Governments and law enforcement agencies will probably try to identify the “command and control” servers from which the malware is being run. If intelligence efforts can pinpoint those and seize control of them, then the encryption keys could be released to all infected networks.
In krijtstreep, altijd hoopvol:
An alternative may be that WannaCry’s operators turn over the keys themselves: the success of the ransomware has made them the top global target for the west’s cyber security community overnight. Even the most hardened criminal organisation is likely to worry about such prominence.
Vandaag:
Wereldwijde gijzelsoftware-aanval stilgelegd: ‘De wereld is gered’
Volgens beveiligingsexpert Ronald Prins van beveiligingsbedrijf Fox-IT is er een manier gevonden om verdere besmetting te voorkomen. ‘De wereld is zo’n beetje gered’, aldus Prins.
De cybersecurity-onderzoeker die de aanval stil heeft weten te leggen ontdekte dat het virus zichzelf uit kan zetten met een ingebouwde ‘kill switch’. Die is geactiveerd, waardoor verdere verspreiding van de massale ransomwareaanval waar landen gisteren wereldwijd door werden getroffen is gestopt.
In Fargo’s aflevering S03E03 zat vorige week ook een ‘killswitch’:
Looking for Something Useful to Do With Your Time? Don’t Try This
Invented in the 1950s by an artificial-intelligence expert, the device is known as the “useless machine.” It is typically a small box with an on/off switch and a hinged lid.
Turn on the switch and a lever pops out, turns off the switch, then retreats. That is the machine’s sole purpose: You turn it on, and it turns itself off.
Verhaal erachter volgens het Wall Street Journal - de ene deftige krant na de ander citeren::
Inventors Dream Up Machines That Exist Only to Turn Themselves Off; ‘Unspeakably Sinister’
The brains behind the original machine is Marvin Minsky, a professor emeritus at the Massachusetts Institute of Technology. Back in 1952 as a graduate student, he spent a summer at Bell Labs, the intellectual hive known for cranking out Nobel laureates.
Mr. Minsky’s job there was nebulous, he says today. "I got there and a manager said, ‘Don’t work on anything that will take less than 30 years—we like to take a long view.’ "
On a lark, Mr. Minsky spent some time “inventing useless things,” he says, such as a “gravity machine,” a device that would ring a bell if the force of gravity changed. The bell never rang. The force of gravity is a “basic physical constant,” Mr. Minsky, 85, explains.
He also dreamed up the useless machine, although the name he gave it was the “ultimate machine.” His mentor at Bell Labs, Claude Shannon, built one and kept it on his desk, where the science-fiction writer Arthur C. Clarke spotted it one day.
In zijn tijd nog geen ‘ransomware’:
“There is something unspeakably sinister about a machine that does nothing—absolutely nothing—except switch itself off,” Mr. Clarke later wrote, saying he had been haunted by the device.
Schepje er boven op:
The Freudian Robot: Digital Media and the Future of the Unconscious
Like all works of art, this machine tells us something about ourselves and our world.
Clarke notes the devastating effect of the Ultimate Machine on nearly everyone who came in contact with it and adds that even “distinguished scientists and engineers have taken days to get over it. Some have retired to professions which still had a future, such as basket-weaving, bee-keeping, truffle-hunting or waterdivining.”
Los hiervan, altijd al een dingetje geweest, bleef die brug nou open of was de brug dicht?
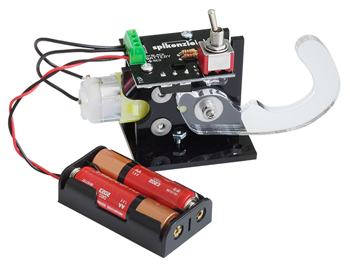
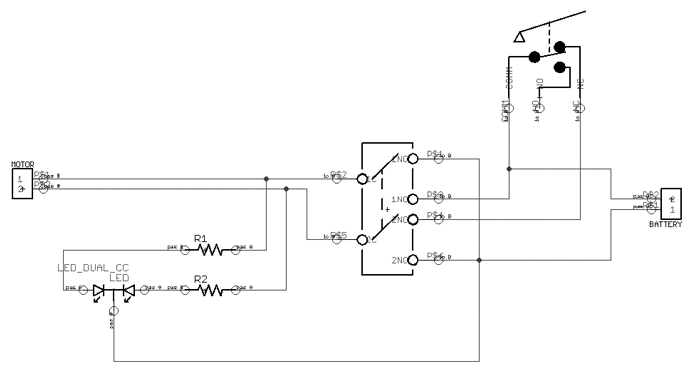
Zie vraag 147 bij Taaladvies.net ![]() maar anders een Do-It-Yourself Kit:
maar anders een Do-It-Yourself Kit:
Voor 18 dollar kan je de logica nu omkeren, even een brandlucht en dan voorgoed uit: